A) lower the Security Status thresholds
B) raise the Security Status thresholds
C) change the Notifications setting to "Show all notifications"
D) change the Action Summary display to "By number of computers"
F) B) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A Symantec Endpoint Protection 12.1 (SEP) administrator deployed SEP clients, but the SEP clients are failing to register with the Symantec Endpoint Protection Manager (SEPM) . Which solution would allow the clients to register with the SEPM?
A) Disable the firewall on the SEP client.
B) Allow port 8014 through the network firewall between the SEPM and the client.
C) Modify the network firewalls so that stateful packet inspection is performed.
D) Open the ephemeral TCP ports on the SEP client firewall.
F) A) and B)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Which Symantec Endpoint Protection 12.1 feature allows an administrator to prevent users from downloading files that are unsafe?
A) SONAR
B) Insight
C) Application Control
D) Trusted Web Domain exceptions
F) A) and B)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A system running Symantec Endpoint Protection is assigned to a group with client user interface control settings set to mixed mode with Auto-Protect options set to Client. The user on the system is unable to turn off Auto-Protect. What is the likely cause of this problem?
A) Tamper protection is enabled.
B) System Lockdown is enabled.
C) Application and Device Control is configured.
D) The padlock on the enable Auto-Protect option is locked.
F) None of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Employees of an accounting company often take their notebooks to customer sites. The administrator needs to apply a different firewall policy when the notebooks are disconnected from the accounting company's network. What must the administrator configure to use the two different policies?
A) Groups
B) Domains
C) Sites
D) Locations
F) None of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A company has three groups of clients: Laptops, Desktops, and Servers. Administrators must have the ability to perform manual scans for these clients from the Symantec Endpoint Protection Manager. In addition, the manual scans need to be customized according to the different clients, for example by customizing whether memory is scanned and which folder locations are scanned. How can the environment be configured to provide this ability while minimizing management overhead?
A) Configure one Virus and Spyware Protection policy with a customized On-Demand scan and set different Exception policies for each group.
B) Configure one Virus and Spyware Protection policy with three customized On-Demand scans.
C) Configure one Virus and Spyware Protection policy with three customized Scheduled scans and setting the schedule to Manual.
D) Configure a different Virus and Spyware Protection policy for each group with customized On- Demand scans.
F) None of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Some customers report that when they run the command "smc -stop" on their clients, they are unable to connect to network resources. What is wrong?
A) The customers need to enable the Smart DHCP option in their firewall policy.
B) The security option "Block all traffic until the firewall starts and after the firewall stops" is enabled.
C) A location awareness policy has been configured that applies when the service is stopped.
D) The network card is blocked by a Device Control policy.
F) None of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A Symantec Endpoint Protection (SEP) administrator creates a firewall policy to block FTP traffic and assigns the policy to all of the SEP clients. The network monitoring team informs the administrator that a client system is making an FTP connection to a server. While investigating the problem from the SEP client GUI, the administrator notices that there are zero entries pertaining to FTP traffic in the SEP Traffic log or Packet log. While viewing the Network Activity dialog, there is zero inbound/outbound traffic for the FTP process. What is the most likely reason?
A) The block rule is below the blue line.
B) The server has an IPS exception for that traffic.
C) Peer-to-peer authentication is allowing the traffic.
D) The server is in the IPS policy excluded hosts list.
F) None of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Which two options are available when configuring DNS change detected for SONAR? (Select two.)
A) Block
B) Active Response
C) Quarantine
D) Log
E) Trace
G) C) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A large-scale virus attack is occurring and a notification condition is configured to send an email whenever viruses infect five computers on the network. A Symantec Endpoint Protection administrator has set a one hour damper period for that notification condition. How many notifications does the administrator receive after 30 computers are infected in two hours?
A) 1
B) 2
C) 6
D) 15
F) C) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A Symantec Endpoint Protection Manager (SEPM) administrator is importing from an Active Directory environment. The administrator needs to know which object types are being imported. Which two object types are imported into the SEPM from Active Directory? (Select two.)
A) policy
B) users
C) computers
D) services
E) groups
G) C) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
An administrator gets a browser certificate warning when accessing the Symantec Endpoint Protection Manager (SEPM) Web console. Where can the administrator obtain a self-signed certificate to prevent this warning from appearing?
A) SEPM console Licenses section
B) Symantec Protection Center
C) SEPM Web Access
D) Symantec Support
F) B) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Refer to the exhibit. 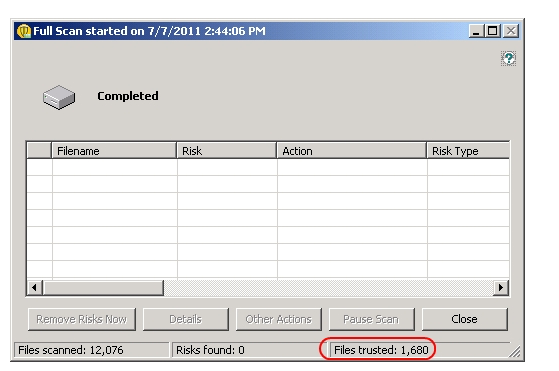 Which settings can impact the Files trusted count?
Which settings can impact the Files trusted count?
A) SONAR settings in the Virus and Spyware Protection policy
B) System Lockdown Whitelist in the Application and Device Control policy
C) Insight settings in the Virus and Spyware Protection policy
D) File Cache settings in the Virus and Spyware Protection policy
F) All of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A financial company has a security policy that prevents banking system workstations from connecting to the internet. Which Symantec Endpoint Protection 12.1 protection technology will be prevented from working on the company's workstations?
A) Insight
B) Application and Device Control
C) Network Threat Protection
D) LiveUpdate
F) None of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Which two criteria can an administrator use to determine hosts in a host group? (Select two.)
A) Subnet
B) Network Services
C) Application Protocol
D) DNS Domain
E) Network Adapters
G) A) and E)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A company is currently testing Symantec Endpoint Protection 12.1 on 100 clients. The company has decided to deploy SEP to an additional 20,000 clients. They are concerned about the number of clients supported on a single Symantec Endpoint Protection Manager (SEPM) . What should the company do to ensure that the SEPM can support the clients?
A) Configure the clients for Pull mode.
B) Decrease the heartbeat interval.
C) Switch to HTTPS for client communications.
D) Switch to IIS as the web server.
F) A) and B)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A company is running the Symantec Endpoint Protection 12.1 firewall and wants to ensure that DNS traffic is allowed. Which feature should be enabled in the firewall policy?
A) DNS exception
B) DNS Lookup
C) Reverse DNS Lookup
D) Smart DNS
F) B) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Which client log shows that a client is downloading content from its designated source?
A) Risk Log
B) System Log
C) SesmLu.log
D) Log.LiveUpdate
F) A) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
An administrator is re-adding an existing Replication Partner to the local Symantec Endpoint Protection Manager site. Which two parameters are required to re-establish this replication partnership? (Select two.)
A) remote server IP Address and port
B) remote site Encryption Password
C) remote site Domain ID
D) remote server Administrator credentials
E) remote SQL database account credentials
G) B) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
An administrator is modifying a Virus and Spyware Protection policy for a Symantec Endpoint Protection 12.1 (SEP) client because it is demonstrating poor boot performance. Which option should the administrator consider to alleviate this problem?
A) Ensure that Risk Tracer is disabled.
B) Load Auto-Protect during the startup of SEP.
C) Enable File Cache across reboots.
D) Modify the policy to use Insight Cache.
F) C) and D)
Correct Answer

verified
Correct Answer
verified
Showing 81 - 100 of 165
Related Exams